Your email address is a digital fingerprint that can compromise your privacy and security. A temporary email service provides a disposable, anonymous address that acts as a protective shield, preventing spam, data harvesting, and identity theft by isolating your primary identity from low-trust online interactions. Learn how these simple tools create a crucial barrier between your real self and the risky corners of the internet. This guide covers exactly how, when, and why to use temporary email for robust online privacy.
Key Takeaways
- Anonymity First: Temporary email allows you to interact online without revealing your primary, personally identifiable email address.
- Spam Prevention: By using a disposable address for sign-ups and downloads, you keep promotional and malicious emails out of your permanent inbox.
- Data Breach Isolation: If a website using your temp mail is hacked, your main email and linked accounts remain safe and unaffected.
- Cost-Effective Privacy: Most temporary email services are free, offering a zero-cost layer of security for everyday browsing.
- Not for Everything: Temporary email should never be used for critical accounts (banking, main cloud storage) or services requiring ongoing identity verification.
- Provider Choice Matters: Select reputable services with clear privacy policies, HTTPS encryption, and reasonable address lifespans for your needs.
[FEATURED_IMAGE_PLACEHOLDER]
📑 Table of Contents
- What is Temporary Email? Understanding the Disposable Inbox
- The Invisible Threat: Why Your Personal Email is a Privacy Liability
- How Temporary Email Creates a Protective Barrier
- Practical Applications: When to Use a Disposable Email Address
- Choosing the Right Temporary Email Service: What to Look For
- The Limitations and Critical Best Practices for Safe Use
- Conclusion: Embracing Proactive Privacy in a Data-Driven World
What is Temporary Email? Understanding the Disposable Inbox
Imagine you need to download a free ebook or access a gated article. The website asks for your email address. You hesitate. That email is linked to your bank accounts, social media, and countless other services. Handing it over feels like giving a stranger a key to your digital life. This is where temporary email, often called disposable or temp mail, enters the picture as a simple yet powerful privacy tool.
A temporary email service provides you with a random, functioning email address that exists for a short, predetermined time—usually a few hours to a few days. You can use this address to receive a single verification email or download link. Once its purpose is served or its time expires, the address and all its messages are permanently deleted from the server. It’s like using a burner phone for a specific call; after the call, the number is gone.
How Does It Work? The Mechanics of a Disposable Address
The process is intentionally straightforward. You visit a temporary email provider’s website. Instantly, the system generates a random email address for you, often something like [email protected]. This address appears on the page, and you’re given a public inbox that automatically displays incoming emails. You copy this address, paste it into the website you’re interacting with, and wait. When the verification email arrives, it pops up right on the provider’s page. You click the link or copy the code, complete your task, and then simply close the browser tab. The address vanishes from circulation.
There’s no password, no lengthy sign-up process, and no persistent account. The entire system is built for ephemeral use. Advanced services might offer a slightly longer lifespan (e.g., 10 days) or the ability to manually refresh the address, but the core principle remains: temporary email is designed for one-off, low-stakes communication where you don’t want to compromise your permanent identity.
The Invisible Threat: Why Your Personal Email is a Privacy Liability
To understand the value of temporary email, you must first understand the immense value—and risk—of your primary email address. It is far more than a communication tool; it is a master key and a tracking beacon.
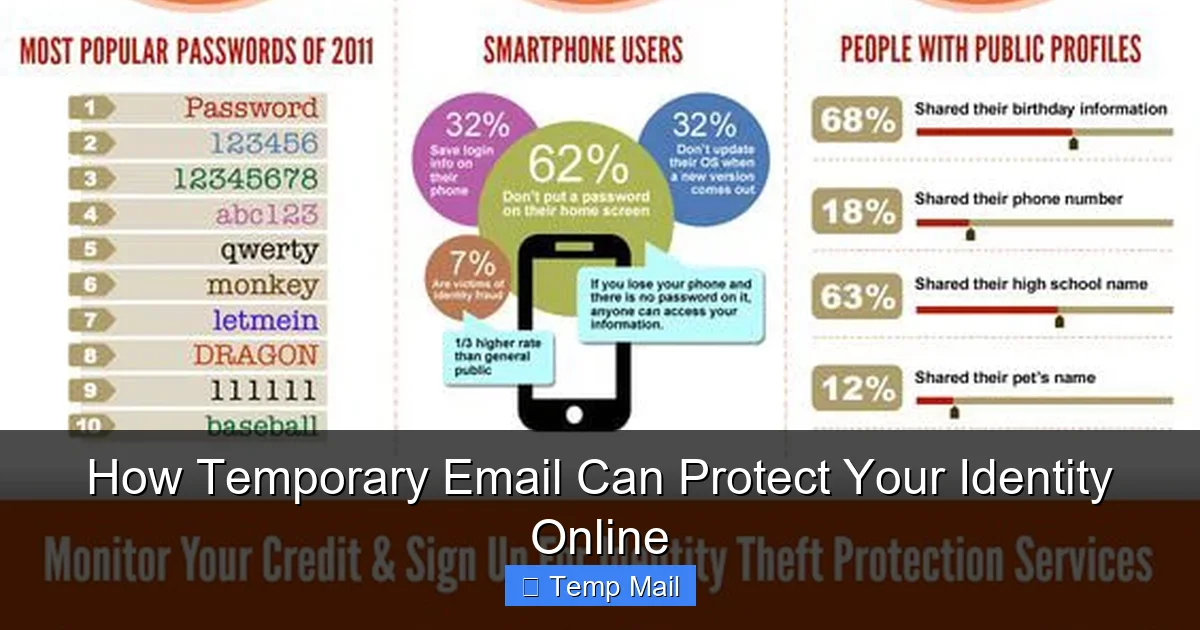
Visual guide about How Temporary Email Can Protect Your Identity Online
Image source: imcgrupo.com
The Email Address as a Digital Skeleton Key
Think about your main email. You use it to reset passwords for your social media, streaming services, online banking, and work applications. A hacker who gains control of that email can potentially lock you out of all those accounts by initiating password resets. It’s the central hub of your digital identity. Because of this, data brokers and malicious actors prize email addresses. They are sold and traded in bulk on the dark web, often for pennies per thousand. Once your email is out there, it’s nearly impossible to recall.
The Spam Feedback Loop
Every time you enter your email on a questionable website, you’re often agreeing, buried in the terms of service, to allow them to share your data with “partners.” These partners send marketing emails. Some of these marketing emails contain tiny, invisible tracking pixels that report back to the sender when you open the email, what device you used, and your approximate location. Your single email address can thus become a source of relentless spam and a tool for your behavioral profiling. The more places you use it, the more this feedback loop spins, filling your primary inbox with clutter and exposing your habits to unknown entities.
How Temporary Email Creates a Protective Barrier
This is where the magic happens. By substituting a disposable address for your real one, you erect a critical firewall between your trusted identity and the untrusted web.
Visual guide about How Temporary Email Can Protect Your Identity Online
Image source: static.vecteezy.com
Anonymity and the Reduction of Digital Footprint
When you use a temp mail address, the website you’re signing up for has no direct, persistent link to you. They have an inbox that might receive a verification email, but that inbox is not tied to your name, phone number, or any other account. After you use it, the connection is severed. This drastically reduces the size of your permanent digital footprint. Data brokers compiling profiles based on email activity will have a gaping hole where your temp mail activities should be. They cannot link those disparate, short-lived actions back to the real you.
Spam Containment and Inbox Sanity
The most immediate benefit is a clean primary inbox. That free webinar you signed up for? The promo codes from a sketchy store? The “urgent” newsletter from a site you visited once? All of that traffic is directed to the temporary address, which self-destructs. Your main inbox remains a sanctuary for emails from friends, family, colleagues, and services you genuinely trust. This isn’t just about annoyance; it’s about security. Phishing emails often masquerade as legitimate marketing. A cluttered inbox increases the chance you’ll click a malicious link by mistake.
Containing the Fallout from Data Breaches
Data breaches are a matter of “when,” not “if.” Major companies, from social networks to retail giants, suffer breaches that leak user databases containing email addresses, passwords, and personal information. If you used your primary email to sign up for a service that gets breached, your email is now in a hacker’s hands. This is a catastrophic starting point for credential stuffing attacks (where hackers try that email/password combo on other sites). If, however, you used a temporary email for that breached service, the leaked email address is meaningless. It points to a dead-end inbox. Your primary accounts remain insulated. The breach affects you only in that you may need to recreate an account on that specific defunct service, not that your entire digital life is at risk.
Practical Applications: When to Use a Disposable Email Address
Knowing the theory is one thing; applying it is another. Here are the most common and effective scenarios for deploying temporary email.
Visual guide about How Temporary Email Can Protect Your Identity Online
Image source: handsofsupport.com
Gated Content and One-Time Downloads
This is the classic use case. You want a whitepaper, a research report, a template, or a discount code. The website asks for an email. Use a temp mail address. Retrieve the file or code via the disposable inbox, and then forget about it. There is no reason for a content marketer to have your permanent email if you only wanted that single asset.
Signing Up for Low-Trust or Unknown Services
Are you trying a new social app, a forum, or a software tool that you’re not sure you’ll stick with? Use temporary email. If the service turns out to be spammy, insecure, or you simply lose interest, you haven’t compromised your main identity. You can walk away cleanly without a trail of marketing emails or a potential data-mining profile linked to you.
Forum Registrations and Commenting
Many online forums and news sites require registration to comment or view threads. These platforms can be hotbeds for spam and data harvesting. Using a temp mail protects you from the forum’s own newsletters and from any potential breach of their user database. It also prevents your commenting history from being easily tied back to your primary email by anyone who might be monitoring.
Accessing Public Wi-Fi and Creating Throwaway Accounts
When using an airport or coffee shop Wi-Fi that requires an email sign-up, use a disposable address. This prevents the venue (or a malicious actor on the same network) from collecting your email for their own marketing or, worse, for targeting you later with phishing campaigns pretending to be from that venue.
Testing and Development
Developers and QA testers use temporary email services to quickly create test accounts for applications without polluting their work or personal inboxes. It’s a clean, efficient way to generate numerous test profiles.
Choosing the Right Temporary Email Service: What to Look For
Not all temp mail providers are created equal. While the core function is similar, features and reliability vary. Here’s what to consider.
Lifespan and Auto-Deletion Policy
How long does the address last? Some expire after 10 minutes, others after 24 hours, and some offer a week. Choose based on your need. For a quick verification code, 10-30 minutes is fine. For a service you might use for a couple of days, a longer lifespan is better. Crucially, ensure the provider automatically and permanently deletes all emails and the address itself after expiration. Manual deletion options are a plus.
Security and Privacy Practices
Look for services that use HTTPS encryption (the padlock in your browser). Read their privacy policy, even if briefly. Do they log IP addresses? Do they claim to not store messages? The best ones explicitly state they do not keep records. Avoid any service that requires you to create an account—that defeats the purpose of anonymity.
Domain Reputation and Reliability
Some temporary email domains are blacklisted by major services (like Gmail or Outlook) because they are abused by spammers. If the provider’s domain is on a blacklist, the verification email you’re waiting for might never arrive because it gets blocked as spam. Use well-known, established providers (e.g., Temp-Mail, 10MinuteMail, Guerrilla Mail). They work hard to maintain deliverability.
Additional Features
Some services offer useful extras: the ability to choose your own inbox name (e.g., [email protected] instead of random characters), multiple language support, or browser extensions that make generating a new address even faster. These are conveniences, not essentials, but they improve user experience.
The Limitations and Critical Best Practices for Safe Use
Temporary email is a powerful tool, but it has clear boundaries. Using it incorrectly can backfire.
What Temporary Email is NOT For
Never use a disposable email for any account that involves real-world identity, finance, or long-term commitment. This includes: online banking, investment accounts, primary cloud storage (like your main Google Drive or iCloud), government services, your primary social media accounts, or any service where you might need to recover access years later. If the service is important, your primary email is required. Temp mail is for the transient, the trivial, and the suspicious.
Understanding the Risks: Deliverability and Account Recovery
The main risk is that some websites actively block known temporary email domains from signing up. They do this to reduce spam and fraud. If you encounter this, you’ll need to use your real email or find a different provider. Another risk is account recovery. If you sign up for a service with a temp mail and later forget your password, you cannot recover the account because you no longer have access to that inbox. You will have to create a new account. This is acceptable for throwaway services but disastrous for important ones.
Best Practices for Effective and Safe Use
- Use Different Providers for Different “Personas”: Use Provider A for newsletter sign-ups, Provider B for forum registrations. This makes it harder to link your activities together even across disposable addresses.
- Never Use Your Real Name: If the service allows you to customize the inbox name (e.g., [email protected]), avoid it. Use random strings to maximize anonymity.
- Check the Lifespan: Before using a temp mail, note how long it will last. If you need the email for more than 10 minutes, don’t use a 10-minute mail service.
- Assume It’s Public: While you have the inbox open, treat it like a public terminal. Don’t access sensitive documents through it, and close the tab as soon as you’re done.
- Combine with a Password Manager: For services you sign up for with temp mail, use a unique, strong password generated by your password manager. This way, even if that service is breached, the password is useless elsewhere.
Conclusion: Embracing Proactive Privacy in a Data-Driven World
Your email address is the skeleton key to your digital life. Handing it out carelessly is like leaving your house keys under the doormat for anyone to find. Temporary email services are not a panacea for all privacy ills, but they are an incredibly effective, simple, and free tool for a specific and critical job: isolating your core identity from the vast, unvetted expanse of the web.
By adopting the habit of using disposable addresses for any non-essential sign-up, you take a powerful proactive step. You declutter your primary inbox, you insulate yourself from the cascading effects of data breaches, and you make yourself a far less valuable target for data brokers and spammers. In an online ecosystem designed to harvest your information, a temporary email is a small act of digital defiance. It’s a reminder that you don’t have to pay with your personal data for every free service or piece of content. Start using one today for your next download or forum sign-up. Experience the immediate relief of a cleaner inbox and the profound peace of mind that comes from knowing your primary identity is that much safer.
Frequently Asked Questions
Is using temporary email legal?
Yes, using temporary email is completely legal. It is simply a tool for receiving email without long-term commitment. It becomes illegal only if used for fraudulent activities, to evade law enforcement, or to circumvent terms of service in a criminal manner, just as with any other communication tool.
Can my temporary email activity be traced back to me?
Generally, no. Reputable temporary email services do not require personal information to generate an address and do not keep logs linking your IP address to a specific disposable inbox. However, if you use the temp mail while logged into your Google account, your browsing activity could be associated with your Google profile by Google itself. For true anonymity, use your browser’s incognito/private mode.
How long do temporary email addresses last?
It varies by provider. Some last just 10 minutes, perfect for a single verification code. Others last 1 hour, 10 hours, or up to 1-2 days. Some services offer a week or until you manually delete it. Always check the provider’s policy before using it for a task that might take longer.
Are temporary email services secure?
Security varies. Look for services that use HTTPS encryption. Understand that the inbox is not private; anyone with the URL can see the emails. Therefore, never use temp mail for sensitive communications. The security benefit comes from anonymity and isolation, not from encrypting message content.
What’s the difference between temporary email and a regular email alias?
A regular email alias (like Gmail’s “+” trick or Outlook aliases) is still tied to your main, permanent email account. All mail sent to the alias forwards to your primary inbox, and you manage it from there. A temporary email is a completely separate, isolated inbox that is deleted after use. The alias is for organization; temp mail is for isolation and destruction.
What is the absolute best use case for temporary email?
The single best use case is for any online interaction where you do not intend to have an ongoing relationship with the service. This includes downloading a free resource, signing up for a one-time webinar, registering on a forum to post a single question, or accessing a site that requires an email just to bypass a gate. If you wouldn’t give the service your phone number, you probably shouldn’t give it your permanent email either.