Tired of your primary inbox being bombarded with spam and targeted ads? A temp mail secure inbox acts as your personal digital shield, providing a disposable email address for any online activity. It’s the simplest, most effective tool to instantly separate your important communications from the Wild West of the web, protecting your identity and keeping your permanent email pristine and private.
Remember the last time you downloaded a free PDF, signed up for a webinar, or commented on a news article? You likely typed in your trusted, personal email address without a second thought. That simple action is a digital handshake, handing over a key to your online identity. That key can be copied, sold, leaked, or used to track your behavior across the internet. What if there was a simpler way? What if you could have a dedicated, disposable email address for these exact moments—a secret, secondary identity for the web? This is the power of a temp mail secure inbox. It’s not just a convenience; it’s a fundamental tool for taking back control of your digital footprint and maximizing your online privacy in an era of constant data harvesting.
This guide will walk you through everything you need to know about using temporary email services securely and effectively. We’ll move beyond the basic “get a random email” concept and dive deep into how a properly used temp mail secure inbox becomes a cornerstone of a smart, private, and spam-free digital life. From understanding the underlying technology to mastering best practices, you’ll learn how to deploy this tool like a privacy professional.
Key Takeaways
- Instant Privacy Barrier: A temp mail secure inbox creates an immediate, throwaway layer between your real identity and the websites, forums, or downloads you engage with online.
- Spam & Scam Defense: By using a disposable address for non-essential sign-ups, you permanently prevent promotional emails, phishing attempts, and malware links from ever reaching your primary inbox.
- No Personal Data Required: Reputable services require no registration, phone number, or personal details to generate an inbox, ensuring your anonymity from the moment you create the address.
- Automatic Cleanup: These inboxes are designed to self-destruct after a set period (e.g., 24 hours, 7 days), automatically deleting all messages and the address itself with no action needed from you.
- Versatile & Cost-Free: Ideal for one-time downloads, forum registrations, app trials, and any situation where an email is a required gatekeeper but you trust the source implicitly.
- Not for Critical Accounts: Never use a temp mail for banking, primary social media, or any account requiring long-term access and password recovery, as the inbox and its contents are temporary.
- Choose Secure Providers: Opt for services that use HTTPS encryption, have clear privacy policies (no logging), and offer features like email forwarding if you need to receive a specific verification code.
📑 Table of Contents
- What Exactly is a Temp Mail Secure Inbox?
- How a Temp Mail Secure Inbox Supercharges Your Online Privacy
- Practical Use Cases: When and How to Use Your Temp Mail
- Security Features to Look For in a Temp Mail Provider
- Common Pitfalls and Limitations to Avoid
- The Future of Temporary Email and Digital Identity
- Conclusion: Your Inbox, Your Rules
What Exactly is a Temp Mail Secure Inbox?
At its core, a temp mail secure inbox is a service that provides you with a random, functional email address for a limited time. It’s also called disposable email, throwaway email, or fake email. But the term “secure inbox” is the crucial part. Not all temporary email services are created equal. A basic, unsecured service might give you an address, but it could log your IP, store messages in plain text, or have lax security. A temp mail secure inbox prioritizes encryption, anonymity, and automatic deletion.
The Technology Behind the Disposability
These services work by maintaining a pool of domain names and generating unique inboxes on their servers. When you visit the site, it assigns you an address like [email protected]. Any email sent to that address lands in a web-based inbox you can access via the service’s interface. The magic is in the impermanence. The server is configured to automatically purge all inboxes after a predefined expiration period—often 24 hours, 48 hours, or up to 7 days. After that, the address is recycled back into the pool, and the data is gone forever. This ephemeral nature is what makes it so powerful for privacy.
Secure vs. Insecure Temporary Email: The Critical Difference
Imagine two scenarios. In the first, you use a free temp mail site that shows ads everywhere, has no HTTPS padlock, and its privacy policy says it “may” collect usage data. Your activity on that site, and potentially the emails you receive, could be tracked. In the second, you use a temp mail secure inbox from a provider that uses end-to-end encryption, has a strict no-logs policy, and operates over secure connections. The second option ensures that even the service provider cannot link your temporary activity to your real identity. The “secure” designation means the service itself is designed to be a privacy vault, not just a temporary mailbox.
How a Temp Mail Secure Inbox Supercharges Your Online Privacy
Your personal email address is often the master key to your online identity. It’s used for account verification, password resets, and marketing profiles. Every time you share it, you create a permanent data point. A temp mail secure inbox breaks this chain of association. Let’s break down the privacy benefits.

Visual guide about Maximize Your Online Privacy with Temp Mail Secure Inbox
Image source: vision-crm.com
1. The Ultimate Spam and Phishing Firewall
Think of your primary email as your home address. You wouldn’t give it out to every random store clerk. A temp mail is like a PO Box you use for all the junk mail subscriptions. When that PO Box gets flooded, you simply close it. By using a disposable address for any website you’re mildly curious about but don’t fully trust, you ensure all their promotional blasts and malicious links are sent to an inbox that will vanish. This means zero spam in your real inbox and a dramatically reduced risk of clicking a phishing email that appears to be from “your bank” but is actually a scam sent to an old temp address you used on a compromised forum years ago.
2. Preventing Data Broker Profiling and Cross-Platform Tracking
Data brokers buy and sell information about you. A major source of this data is your email address, which acts as a persistent identifier linking your activity across thousands of websites. If you use the same email to sign up for a gardening forum, a car-buying site, and a news outlet, those entities (and the brokers they sell to) can build a surprisingly accurate profile of your interests, location, and demographics. Using a unique temp mail secure inbox for each of these sites severs that link. Each disposable address is an isolated, anonymous data point that expires before it can be sold or aggregated, making you a much less valuable target for profiling.
3. Shielding Yourself from Data Breaches
We read about them constantly: a major company’s database is hacked, and millions of user emails, passwords, and other details are leaked onto the dark web. If you used your primary email for that service, your address is now in the hands of cybercriminals, leading to targeted attacks, credential stuffing (where hackers try your email/password combo on other sites), and a lifetime of increased risk. Had you used a temp mail secure inbox for that one-time sign-up? The leaked data contains a dead, meaningless address that expires in 24 hours. The breach has zero impact on your real identity.
Practical Use Cases: When and How to Use Your Temp Mail
Knowing the theory is great, but knowing when to pull the trigger is what makes this tool effective. Here are the prime scenarios where a temp mail secure inbox is not just helpful, but essential.

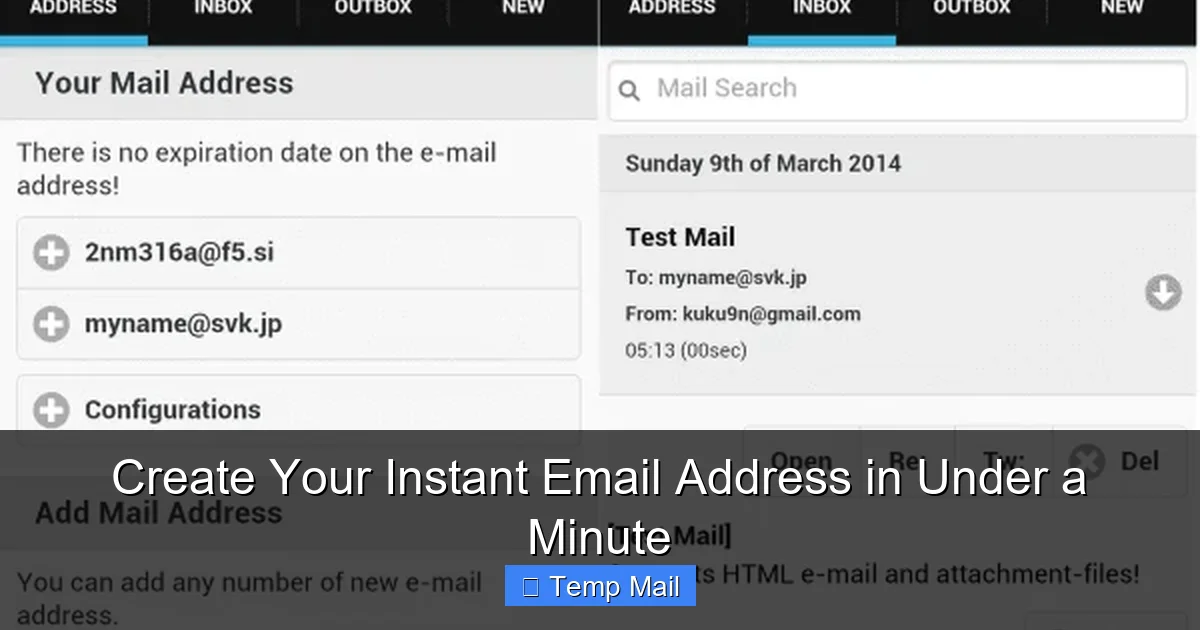
Visual guide about Maximize Your Online Privacy with Temp Mail Secure Inbox
Image source: anonymmail.net
For One-Time Downloads and Content Gates
How many times have you wanted a free e-book, template, or software trial, only to be stopped by a form demanding your email? This is a classic lead generation tactic. The company will likely send you a download link, but they’ll also add you to their marketing list, and that email address could be shared. Use your temp mail here. Get the file you need, and let the inbox expire. No clutter, no follow-ups, no risk.
Navigating Forum and Comment Section Registrations
You want to ask a quick question on a niche forum or leave a comment on a controversial news article. These platforms often require registration. Do you really want that site, and its potentially toxic user base or aggressive advertising partners, to have your permanent email? Using a temp mail secure inbox creates a clean separation. You can participate, get your answer, and vanish without a trace. The temporary address protects you from any future data leaks from that specific community.
Testing Services and App Trials
Signing up for a 7-day trial of a SaaS tool or a mobile app? Perfect temp mail scenario. You’ll get the initial verification email and can test the service. If you decide not to subscribe, you simply ignore the follow-up “your trial is ending” emails. They go to a dead inbox. This prevents the common pitfall of “I meant to cancel but forgot” because the payment reminder emails will also go to the temp address, giving you a natural, frictionless off-ramp.
Bypassing “Email Required” for Non-Essential Tools
Need to use an online PDF converter, a file compressor, or a simple design tool that insists on an email before letting you download? These are prime candidates. You are not building a long-term relationship with these tools. Use your disposable address to get past the gatekeeper, complete your task, and walk away. The temp mail secure inbox absorbs all the subsequent promotional noise.
Security Features to Look For in a Temp Mail Provider
Not all temp mail services are safe. Some may be fronts for collecting data themselves. To ensure your temp mail secure inbox is actually secure, you must vet the provider. Here are the non-negotiable features.
Visual guide about Maximize Your Online Privacy with Temp Mail Secure Inbox
Image source: mytempmails.com
HTTPS Everywhere and Encryption
This is the absolute baseline. The provider’s website must use HTTPS (the padlock icon in your browser). This encrypts the connection between your browser and their server, preventing eavesdroppers on public Wi-Fi from seeing the emails you receive. Look for mentions of SSL/TLS encryption in their technical or privacy documentation.
Strict No-Logs Policy
A trustworthy provider will explicitly state that they do not log, store, or correlate your IP address with the temporary email addresses they generate. They should not require any personal information to create an inbox. Read the privacy policy carefully. Phrases like “we do not store message content longer than necessary” or “IP addresses are not linked to mailboxes” are good signs. Absolute anonymity is the goal.
Inbox Lifetime and Automatic Deletion
A core feature of a temp mail secure inbox is its self-destruct mechanism. The provider should clearly state how long inboxes remain active (e.g., 10 minutes, 1 hour, 24 hours, 7 days). The best services automatically and permanently delete both the emails and the address itself after this period, with no manual “delete” button required from you. This guarantees no residual data is left behind.
Open-Source Code and Transparency
While not common, some of the most trusted disposable email services open-source their code. This allows the security community to audit it for backdoors, tracking scripts, or vulnerabilities. If a provider is transparent about their infrastructure and code, it’s a strong signal of integrity. Look for GitHub repositories or public security audits.
Common Pitfalls and Limitations to Avoid
A temp mail secure inbox is a powerful tool, but it has clear boundaries. Misusing it can lead to real problems. Understanding these limitations is key to using it wisely.
The Irrecoverable Inbox: You *Will* Lose Access
This is the most critical rule. Once the inbox expires, it is gone. All emails are deleted forever. If you used a temp mail to sign up for an account you actually want to keep (like a social media profile or an online bank), you will be locked out the moment you need to reset your password. The verification email will bounce. You will have no way to recover that account. This is why the golden rule is: Never use a temp mail for any account you need to access long-term or that contains valuable personal or financial information.
Not All Websites Accept Disposable Domains
Many popular platforms (Google, Facebook, Apple, Microsoft, major banks, and most reputable e-commerce sites) actively block known disposable email domains. They do this to prevent fraud, spam, and abuse. If you try to sign up with a temp mail on these sites, you’ll get an error message saying the email is invalid. This is a feature, not a bug—it tells you the site is taking security seriously. Respect this block; trying to circumvent it is often impossible and signals you’re on a platform that values security.
Attachment and Size Limits
Temporary inboxes are designed for text-based verification emails and small files. They almost always have strict limits on attachment size (often just a few megabytes) and may block certain file types entirely for security. Do not expect to receive a large PDF, video, or software installer via your temp mail secure inbox. Use it for what it’s intended: codes, links, and short messages.
The Future of Temporary Email and Digital Identity
The demand for privacy tools like the temp mail secure inbox is growing as data breaches become routine and surveillance capitalism matures. The future will likely see these tools evolve and integrate more deeply with our digital lives.
Integration with Password Managers and Privacy Suites
We are already seeing password managers like Bitwarden and 1Password experiment with built-in “masked email” or alias features that create unique, forwardable email addresses tied to your main account but revocable at any time. This is the logical evolution of the temp mail concept—more seamless, integrated, and managed. These “aliases” often forward to your real inbox, giving you more control than a purely disposable, non-forwarding address.
Enhanced Security Protocols and Decentralization
Future temp mail secure inbox providers may adopt even more robust cryptographic protocols, possibly integrating with decentralized identity systems (like those based on blockchain) to provide verifiable, anonymous credentials without relying on a single central email provider at all. The inbox might become just one component of a broader, user-controlled digital identity stack.
Regulatory Pressures and Industry Adoption
As regulations like GDPR and CCPA enforce stricter data minimization principles, the idea of using minimal, temporary identifiers for non-essential interactions will gain mainstream acceptance. We may see “provide a temporary email” become a standard option on web forms alongside “sign up with Google/Facebook,” officially recognizing the disposable inbox as a legitimate privacy-preserving choice.
Conclusion: Your Inbox, Your Rules
Your email address is more than a communication tool; it’s a fingerprint. Every time you casually hand it over, you leave a trace that can be followed, sold, and exploited. A temp mail secure inbox is your ability to draw a line in the digital sand. It’s the simple act of saying, “For this interaction, my real identity is off the table.” It transforms your online experience from one of passive data surrender to one of active boundary-setting.
Start today. Bookmark a reputable, secure provider. Make it a habit to reach for your temporary email whenever a website asks for an address and you don’t have a long-term, trust-based relationship with it. Use it for the downloads, the forums, the trials, and the content gates. Let your primary inbox become a sanctuary for only the communications you truly value: messages from friends, family, and essential services. By strategically deploying a temp mail secure inbox, you are not just avoiding spam; you are performing a small but powerful act of digital self-defense, reclaiming your privacy one disposable address at a time.
Frequently Asked Questions
Is using a temp mail secure inbox legal?
Yes, using a temporary email service is completely legal in virtually all jurisdictions. It is a legitimate tool for privacy protection. However, using it to commit fraud, evade legal requirements, or send illegal content is, of course, illegal. The tool itself is neutral; its ethical use depends on the user’s intent.
How secure is a temp mail inbox against hackers?
Security varies by provider. A true temp mail secure inbox uses HTTPS encryption and automatically deletes messages, limiting exposure. However, because the inbox is public (anyone with the URL could potentially access it while it exists), it should never be used for sensitive information like passwords, financial data, or private documents. Its security is about anonymity and temporality, not storing secrets.
Can I use a temp mail for account recovery on important sites?
Absolutely not. This is the most critical mistake. If you use a temp mail to sign up for an account (like social media, banking, or cloud storage), you will be unable to recover it if you forget your password, as the recovery email will be sent to an expired, non-existent inbox. Always use your permanent, secure email for any account you need to keep long-term.
What happens to my emails after the inbox expires?
With a reputable temp mail secure inbox service, all emails and the address itself are permanently and automatically deleted from their servers the moment the timer runs out. The data is unrecoverable. The address is then recycled and assigned to a new user. There is no residual data stored.
Are there any risks to using disposable email services?
The primary risk is using an insecure provider that logs your activity or IP address, defeating the privacy purpose. Another risk is user error: accidentally using it for an important account. There is also a minor risk that the service itself could be compromised, but since emails are short-lived, the window of exposure is tiny. Always choose providers with clear, transparent security practices.
What is the best practice for using a temp mail secure inbox?
Follow this simple rule: Use it for anything you don’t need to keep. Sign up for newsletters you’re curious about, download free resources, register for one-time events, or test apps. Never use it for professional, financial, or primary personal accounts. Treat it as a digital “burner phone” for the internet—incredibly useful for specific, temporary tasks, but not for your life’s core communications.